The way we identify and authenticate ourselves online today has barely changed since the inception of the web. We all use passwords, often ones that are easy to guess or crack. And we all reuse and share them, we forget and misplace them. And even if we are careful, some of the sites we use get breached and our accounts and passwords taken.
Meanwhile, the stakes have become much, much higher. Many aspects our life, our belongings, our private information, our interactions, are now online. And as we are moving more of our life online, we are inadvertently creating a digital identity of ourselves that we only control partially: much of it is scattered across hundreds of sites, stored in numerous company databases, and often outdated.

With passwords there is an interesting disconnect between what we advise people to do — follow complex password “recipes”, do not reuse, change frequently, use Two-Factor Authentication (2FA), utilize password managers — and what most people actually feel comfortable doing. And if nothing else, these suggestions make people less confident online, even insecure about their ability to use the services: “Will I lock myself out if I turn on 2FA?” or “Is my password manager now saving this newly generated password?”
Passwords: The Blame Game
What is most disturbing about advice like this, is the insinuation of blame, where if your account gets hacked and your personal identity or assets poached, that you as the owner should have taken more precautions, and surely must not have followed the guidance given. It’s as if you left the key to your house under a flowerpot, or did not lock the door at all, while a fairer analogy would be that your safe at the bank has 24/7 street access and the bank only provided a $1 high school locker padlock.
“online safety is a shared responsibility between the user and the service provider with emphasis on the latter”
Keeping online accounts safe is a shared responsibility, where a large part of the burden rests with the provider of the service who should enable their users to access their accounts in a safe manner. Those enforcing complex password recipes are missing the point here: it is about making it easy for the users to behave in a secure fashion.
Building Authentiq
We started creating Authentiq with asking ourselves a simple question:
“as most of us have our phone within reach all day, and these phones have increasingly more capabilities, why not use our phone to identify and authenticate ourselves to the online services we use everyday?”
Our initial goal is to devise an authentication method that is delightful to use and at the same time keep us more safe than passwords. And being developers ourselves, we want this to be very straightforward to integrate and robust. And on top of that, we believe that your identity should not be stored in some central profile database. So we came up with the following principles:
For everyone, users and developers:
- Drop passwords altogether, your phone is your online ID.
- Use capabilities of your phone: biometrics, sensors, secure elements, notifications.
- No centrally stored profile, your phone is your identity “wallet”.
- High transparency: you can see what information is exchanged with who.
- An open system and architecture, while keeping your information private.
- Easy, delightful and safe UX.
For developers:
- Easy integration, use identity and authentication standards where possible.
- Support existing username and password and offer a painless transition to more safe methods.
- An open system and architecture, verifiable and low dependency.
- Decentral, identity data and transactions should not be stored centrally.
- Open ecosystem where other parties can provide identity services.
Developers are our first priority, as end users of our apps, as users of our authentication methods integrating it in their services, and as partners in our effort to get rid of passwords and help us build open source integrations in various platforms.
Authentiq: How it works
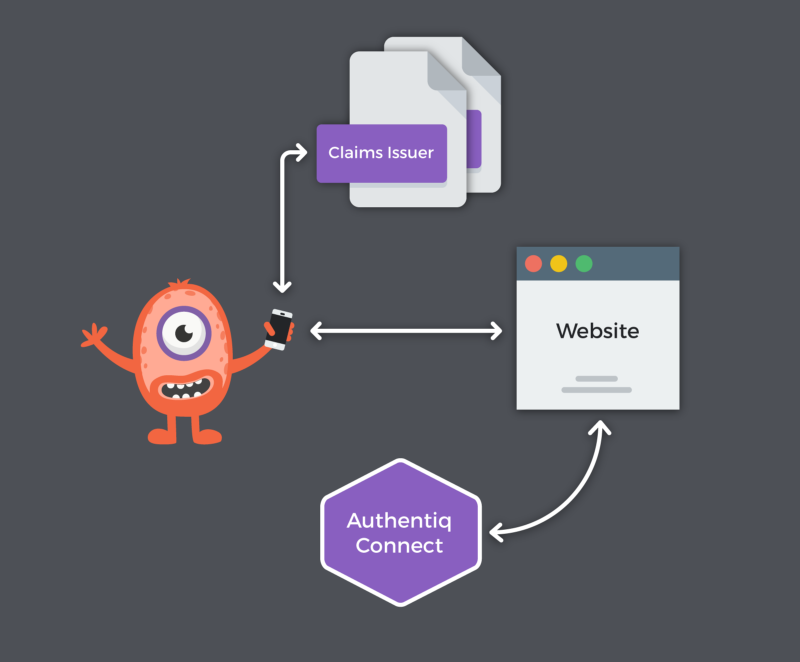
So what we have today are two Authentiq ID apps, one for Android phones and one for the Apple iPhone (iOS), and the Authentiq Connect service that connects your site to the Authentiq ID app on your user’s phone using standards like OAuth and OIDC.
Give it a spin on our GitLab Demo, the latest version of the GitLab with Authentiq enabled. You can either download the the Authentiq ID app first or just have a link sent to you to install it. In the meantime, we answered the most frequently asked questions on this FAQ page.
“User profiles not to be stored centrally”
Authentiq Connect acts as an Identity Provider (IdP) in OIDC terms, but we call it an IdP Bridge as it does not maintain a database of identities, but connects to the identity wallets on the phones instead. We currently run Authentiq Connect as a service, but our goal is to enable developers to run their own instance too, and we aim to open source Authentiq Connect later this year.
The diagram above also depicts a Claims Issuer. This component verifies Identity Claims — e.g. name or email addresses — of the users of the Authentiq ID apps, and sends the cryptographically signed claims to the identity wallet in these apps. But more on this and other details of our architecture in a next post!
The Authentiq team
We’re a small team of developers with a big ambitions: eradicate passwords! Co-founders Pieter and Stan were in two successful startups before, are passionate about security, identity, and UX and are experienced SaaS company builders. They are responsible for most of the backend systems. Chris and Alexander are full stack developers, and responsible for the care and feeding of the Authentiq ID apps and most of the customer facing parts. And Martijn is our pixel magician, our UX and design guy. No marketing and sales, so yes, much to do on that front still.
Contribute
We’re always looking for help. We’re not hiring yet, but if you’d like to work on an integration for one of the many platforms out there, or contribute to the software we open sourced, or in any other way, please do contact us. And if you’re an investor and like to follow our journey, don’t hesitate to connect on AngelList or follow @AuthentiqID on Twitter.